- Sql Injection Tool Get Cc Cvv Dumps List
- Sql Injection Tool Get Cc Cvv Dumps Download
- Sql Injection Tool Get Cc Cvv Dumps Software
- Sql Injection Tool Get Cc Cvv Dumps Code
- Sql Injection Tool Get Cc Cvv Dumps File
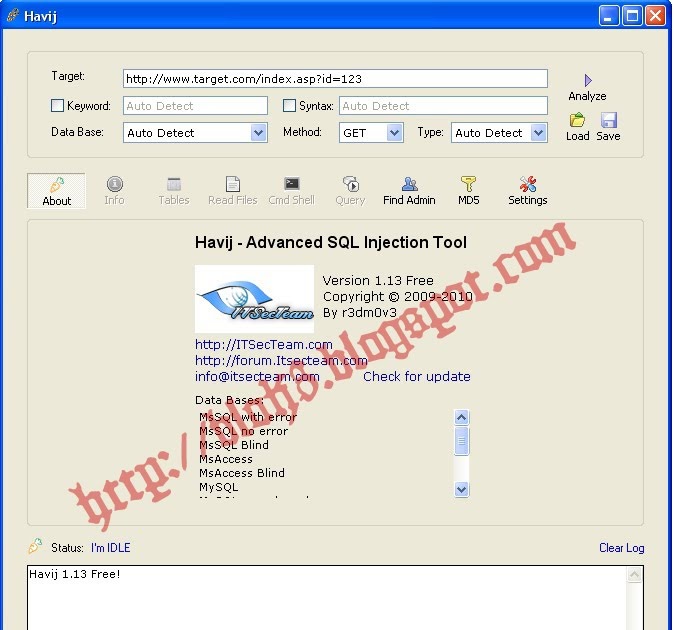
Carding Dorks List 2020 Carding. Dorks is the best method for getting random people's carding information. Upon having the victim's card details one can use his card details to do the unauthorized transactions. Below I'll post the new carding dorks that you can use to get the people's credit card details. Those who wonder what carding. Havij is an advanced SQL injection tool which makes. Now select the Tables with sensitive information and click Get Columns button.After that select the. SQLI Hunter is an automation tool to scan for an Sql Injection vulnerability in a website. Compact penetration testing tool for hacking method of Structure Query Language Injection. Sql Injection Tool Get Cc Cvv Dumps Resident Evil 4 Weapon Mods Pc Download Steinberg Cubase 7 Keygen Free Download Install Ubuntu Dell Venue 8 Pro Resident Evil 4. Sql Injection Tool Get Cc Cvv Dumps Remington 870 Serial Numbers Date Of Manufacture Player Lost In Reality Rar File Bodhi Puja Gatha Pdf Merge Sudden Strike 3 Arms For Victory Maps Teka Nf 340 C Manual Divx 6.9 2 Codec Nesterj Nes Emulator 1 11 Ps Vita Canary Birds Singing Mp3 Download Keygen Dp Animation Maker.
sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. It comes with a powerful detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database, to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
Sql Injection Tool Get Cc Cvv Dumps List
- Full support for MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB, Informix, MariaDB, MemSQL, TiDB, CockroachDB, HSQLDB, H2, MonetDB, Apache Derby, Amazon Redshift, Vertica, Mckoi, Presto, Altibase, MimerSQL, CrateDB, Greenplum, Drizzle, Apache Ignite, Cubrid, InterSystems Cache, IRIS, eXtremeDB, FrontBase, Raima Database Manager, YugabyteDB and Virtuoso database management systems.
- Full support for six SQL injection techniques: boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries and out-of-band.
- Support to directly connect to the database without passing via a SQL injection, by providing DBMS credentials, IP address, port and database name.
- Support to enumerate users, password hashes, privileges, roles, databases, tables and columns.
- Automatic recognition of password hash formats and support for cracking them using a dictionary-based attack.
- Support to dump database tables entirely, a range of entries or specific columns as per user's choice. The user can also choose to dump only a range of characters from each column's entry.
- Support to search for specific database names, specific tables across all databases or specific columns across all databases' tables. This is useful, for instance, to identify tables containing custom application credentials where relevant columns' names contain string like name and pass.
- Support to download and upload any file from the database server underlying file system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
- Support to execute arbitrary commands and retrieve their standard output on the database server underlying operating system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
- Support to establish an out-of-band stateful TCP connection between the attacker machine and the database server underlying operating system. This channel can be an interactive command prompt, a Meterpreter session or a graphical user interface (VNC) session as per user's choice.
- Support for database process' user privilege escalation via Metasploit's Meterpreter
getsystemcommand.
Refer to the wiki for an exhaustive breakdown of the features.
You can download the latest zipball or tarball.
Preferably, you can download sqlmap by cloning the Git repository:
- sqlmap User's manual.
- sqlmap History.
- sqlmap Frequently Asked Questions (FAQ).
- Material around sqlmap presented at conferences.
Watch more demos here. Adobe illustrator cc portable for mac.
All code contributions are greatly appreciated. First off, clone the Git repository, read the user's manual carefully, go through the code yourself and drop us an email if you are having a hard time grasping its structure and meaning.
Bug reports are welcome! Please report all bugs on the issue tracker. Our preferred method of patch submission is via a Git pull request.
Each patch should make one logical change. Please follow the existing stylistic conventions: wrap code to 76 columns when possible. Avoid tabs, use four space characters instead. Before you put time into a non-trivial patch, it is worth discussing it privately by email.
Many people have contributed in different ways to the sqlmap development. You can be the next!

sqlmap is the result of numerous hours of passionated work from a small team of computer security enthusiasts. If you appreciated our work and you want to see sqlmap kept being developed, please consider making a donation to our efforts via PayPal to donations@sqlmap.org or by clicking on the button below.
Sql Injection Tool Get Cc Cvv Dumps Download
We also accept Ƀitcoins to 1AUrrKYsamBEThdruYTQmUfMfLF7aaxU6x.
Copyright © 2006-2021 by Bernardo Damele Assumpcao Guimaraes and Miroslav Stampar. All rights reserved.
This program is free software; you may redistribute and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation; Version 2 (or later) with the clarifications and exceptions described in the license file. This guarantees your right to use, modify, and redistribute this software under certain conditions. If you wish to embed sqlmap technology into proprietary software, we sell alternative licenses(contact sales@sqlmap.org).

This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License v2.0 for more details at http://www.gnu.org/licenses/gpl-2.0.html.
Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program.
- Bernardo Damele A. G. (@bdamele)
- Miroslav Stampar (@stamparm)
You can contact the development team by writing to dev@sqlmap.org.

Bug reports are welcome! Please report all bugs on the issue tracker. Our preferred method of patch submission is via a Git pull request.
Each patch should make one logical change. Please follow the existing stylistic conventions: wrap code to 76 columns when possible. Avoid tabs, use four space characters instead. Before you put time into a non-trivial patch, it is worth discussing it privately by email.
Many people have contributed in different ways to the sqlmap development. You can be the next!
sqlmap is the result of numerous hours of passionated work from a small team of computer security enthusiasts. If you appreciated our work and you want to see sqlmap kept being developed, please consider making a donation to our efforts via PayPal to donations@sqlmap.org or by clicking on the button below.
Sql Injection Tool Get Cc Cvv Dumps Download
We also accept Ƀitcoins to 1AUrrKYsamBEThdruYTQmUfMfLF7aaxU6x.
Copyright © 2006-2021 by Bernardo Damele Assumpcao Guimaraes and Miroslav Stampar. All rights reserved.
This program is free software; you may redistribute and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation; Version 2 (or later) with the clarifications and exceptions described in the license file. This guarantees your right to use, modify, and redistribute this software under certain conditions. If you wish to embed sqlmap technology into proprietary software, we sell alternative licenses(contact sales@sqlmap.org).
This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License v2.0 for more details at http://www.gnu.org/licenses/gpl-2.0.html.
Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program.
- Bernardo Damele A. G. (@bdamele)
- Miroslav Stampar (@stamparm)
You can contact the development team by writing to dev@sqlmap.org.
SQLi Dumper v.9.6 is an excellent, advanced, automatic SQL injection tool for testing links that may contain SQL injection problems in Windows.
Sql Injection Tool Get Cc Cvv Dumps Software
This tool is more powerful than the famous Havij SQL injection and has many features including:
-Supports Multi. Online search engine (to find the trajects);
-Automated exploiting and analyzing from a URL list;
-Automated search for data in a bulk URL list;
-Automated analyzer for injections points using URL, POST, Cookies, UserLogin or UserPassword;
-Dumper supports dumping data with multi-threading (databases/tables/columns/fetching data);
-Exploiter supports up to 100x threads;
-Analyzer and Dumper supports up to 50x threads;
-Advanced WAF bypass methods;
-Advanced custom query box;
-Dumper can dump large amounts of data, with greats control of delay each request (multi-threading);
-Easy switch vulnerabilities to vulnerabilities;
-Supports proxies list;
-GeoIP database;
-Internal database;
-Trash System;
-Admin login finder;
-Hash online cracker;
-Reverse IP;
-Standalone .exe (no install).
Sql Injection Tool Get Cc Cvv Dumps Code
The SQL Injection Methods that are supported include:
– MySQL
– Union (Integer / String)
– Error (Integer / String)
** Error Methods:
– Double Query
– XPATH – ExtractValue
– XPATH – UpdateXML
– Brute Forcing
– Blind
– Load File
– Load File Scanner
** Illegal Mix Of Collations:
– UnHexHex()
– Binary()
– Cast As Char
– Compress(Uncompress())
– Convert Using utf8
– Convert Using latin1
– Aes_decrypt(aes_encrypt())
– MS SQL
– Union (Integer / String)
– Error (Integer / String)
** Illegal Mix Of Collations:
– SQL_Latin1;
– Cast As Char.
– Oracle
– Union (Integer / String)
– Error (Integer / String)
** Error Methods:
– GET_HOST_ADDRESS
– DRITHSX.SN
– GET;APPINGXPATH.
** Illegal Mix Of Collations:
– Cast As Char.
** Suports TOP N Types:
– ROWUM
– RANK()
– DESE_RANK()
** Analizer detects also:
– MS Access
– PostgredSQL
– Sybase
Sql Injection Tool Get Cc Cvv Dumps File
Download from: Mega.nz
